Commercial banks in Vietnam after 15 years of modernizing the bank have basically completed the CoreBank system, card management system, and database storage system for each commercial bank.
In the operation of new products and services and credit, banking security and safety (in terms of technology and technology security by the regulation of operational control rounds) always considered a key task with a key meaning. In addition, the implementation of measures to tighten banking security to prevent criminals from attacking banks also needs its own regulations, contributing to ensuring banking and social order and safety.
I. Commercial banks need to tighten banking security in the last months of 2020
In all conditions, the task of ensuring security and safety of banking activities is always the number one central task. Especially from the beginning of the year until now, in a number of provinces and cities like Khanh Hoa, Bac Giang, Ho Chi Minh City, Ba Ria - Vung Tau, Tien Giang ... branches, bank transaction points.
According to the Ministry of Public Security, the recent bank robberies show that the prevention and self-defense activities of banks are still loopholes and inadequacies; vigilance awareness of officers, staff, bank branch security teams, transaction offices is not high.
After many bank robberies occurred across the country, the State Bank of Vietnam issued Official Letter No. 2903 / TTGSNH1, requesting credit institutions and foreign bank branches to enhance safety at the locations. deal. Being aware of the importance of ensuring security and safety of banking activities in transactions, especially in the context of crimes related to banking activities, there are complicated developments. In order to avoid loss of State assets, credit institutions and the lives of customers, officials, bank employees, to ensure absolute safety and security, especially in cash transactions at branch offices, transaction offices and ATMs of credit institutions' branches and people's credit funds in the country. Especially at the time of the last months of the year, the volume of cash and assets of delivery, preservation, transportation increased, the situation of security and order and social safety had many complicated developments. Units need to strengthen the guarding and protection of branch offices, transaction offices, ATMs to ensure asset safety in vaults, cash transaction places, and money transportation on roads.
II. Strengthen operational security of commercial banks
Commercial banks need to further invest in technology (hardware, software) to ensure security and security by a 3-layer firewall according to international practices on investment in the CoreBank security system and application solutions. Today, hackers "target" ATMs and emails, or attack through users of departments such as counter accountants and tellers to attack the system of commercial banks, although in the past 15 years, the banking industry has constantly improved. high-quality firewall security for CoreBank regularly needs to upgrade the new generation "Firewall", malicious software, solutions to prevent data loss, intrusion detection system; issuing internal regulations and procedures to control information technology activities ...
However, this is still not enough due to the increasing network attacks with unpredictable sophistication with services. such as Internet Banking, Mobile Banking, extending 24/7 ATM service in all 365 days, ... besides utilities also brings many risks and challenges in information security to customers and commercial banks. Recently, hacker groups often used cobalt malware to attack the card system, CoreBanking database store, and ATMs of banks. Hackers often use malicious methods to send "cobalt" to manipulate account information and adjust security settings to be able to withdraw cash via ATM. In addition, cybercriminal groups work together to carry out more sophisticated attacks, such as via email (hidden in spam, phishing personal information of customers to perform fraudulent transactions. , ... On the other hand, the target group of this hacker group is bankers, because if one employee clicks on the email containing malicious code, the malicious code will immediately penetrate into the whole network. In recent years, there have been many crimes with cameras mounted to steal card information from ATM locations to make fake cards and make fraudulent transactions to withdraw money from cardholders at some ATMs of commercial banks. attention, card criminals often choose the time of night or dawn to withdraw money to avoid the attention of cardholders and bank staff, as well as avoid the situation that the cardholder calls card locking switchboard.
III. Should be a plan to invest in equipment and application of network security and security technologies
The current cyber hacking environment is changing and evolving rapidly in terms of the size, speed, and quality of cyberattacks. In order to minimize risks, over the past time, Vietnam has issued a number of Decrees and standards on network information security of the Vietnam Association of Information Security (VNISA), which annually assesses the level of assurance to meet the security of commercial banks. The important issue is that banks must determine their own levels of security, create their own regulations, professional processes, and invest in technology systems, train people in accordance with regulations for each commercial bank. But in fact, only a few banks have defined the level of security for banks at 4/5 and have not implemented drastically, sometimes only at the plan level. The State Bank has issued a document instructing banks to reduce the withdrawal limit or the number of times for each ATM card to be withdrawn within the time frame from 22:00 pm to 5:00 am to avoid risks to customers. However, in reality, the commercial banks' service delivery system has many different objects of protection. Therefore, there will be many different measures to deal with cybersecurity issues such as monitoring of banking transactions, monitoring of Internet Banking, MobiBanking activities ... In addition, commercial banks need to take the following forms. providing information, raising the awareness of customers for the purpose so that customers know how to keep all personal account information confidential, ensuring their transaction channels do not disclose information.
IV. Need to comply with information security, manage risks from losing personal information of customers and banks
The monitoring of security information in the system is really necessary. This will help control a system with many different components managed, centralized alerts and automatically provide analysis and evaluation for each component as well as the overall system in a timely manner. time. Moreover, monitoring allows correlation and sequence of events of many different systems to provide accurate information flow from attacks to determine the source and take remedies. timely. In addition, it is also necessary to warn, measure, manage risks, and manage compliance with business processes such as:
-
Detect security issues and provide time for troubleshooting information security from collecting data from all technology platforms, software, and applications. Correlate events with different contexts, scan for serious incidents, and monitor user behaviors, detect threats from within.
-
Make reports on the compliance of IT systems based on international standards ISO 27001, PCI-DSS, NIST ... automatically or whenever required by the organization. Incident management and organization of events across a set of centralized systems.
-
The main manager and supervisor at the bank should directly manage the system and make sure not to disclose customer information out.
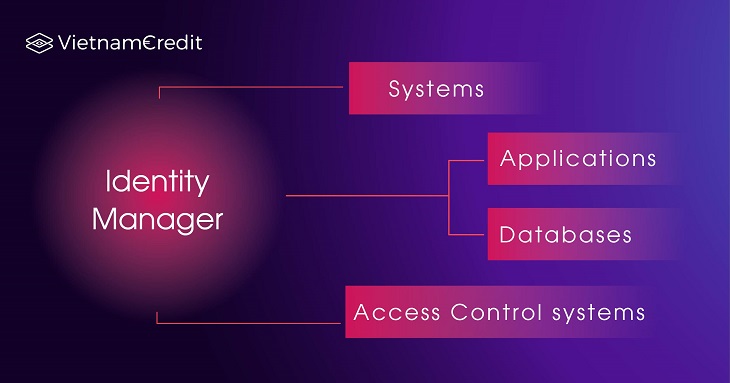
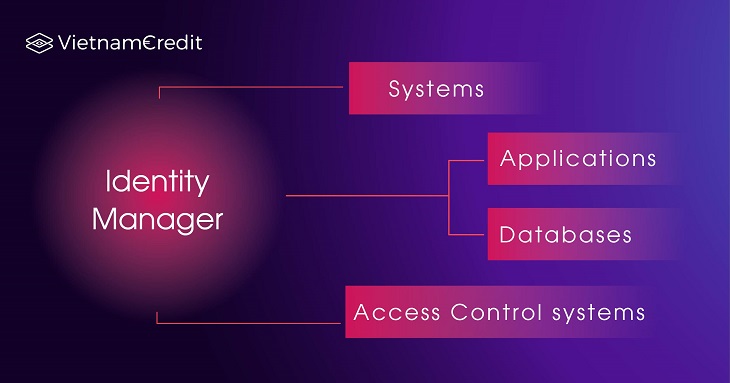
Figure 1: 4 criteria that management need special attention
V. Commercial banks are not particularly concerned about the issue of people and identity in banking security
Account, customer information, transaction password ... are confidential information. Therefore, the administration and monitoring of the information storage area are especially important. Obviously, attackers do not steal each account, each password, but often use administrative accounts, privileged accounts to easily steal confidential information in large quantities. Therefore, make sure that your information technology system is protected against attacks of this type. Commercial banks should pay attention to deploying solutions to manage identities, privileged accounts, and access management for businesses:
-
Standard compliance orientation: High security is the key to technology helping businesses and organizations achieve international standards on information security, bringing trust to customers and partners in business.
-
Better business: Improve business compliance in production and business with only one access point to sensitive assets and automatically manage privileged access accounts.
-
Easy to manage application access (hardcoded, embedded credentials) in many hardware environments, software, and virtualization.
-
Isolate and protect important IT assets from administrative users, infected endpoints, backdoors ...
-
Compliance report for Sarbanes Oxley, PCI, and Basel II standards for information technology systems of enterprises.
-
Minimize external and internal threats: Control administrative users' access to highly sensitive assets, define and enforce unified security policies for Manage privileged identities of the whole system.
-
Real-time control of all administrator sessions, in encoded video format.
Complied by Vietnam Credit